The arrest of an individual in the United States on charges of conspiring to export defense-related technologies to Sudan for use by the Iranian government exposes a sophisticated procurement architecture designed to bypass the International Traffic in Arms Regulations (ITAR). This is not merely a criminal incident; it is a case study in the asymmetric logistics of sanctioned states. Proliferation networks do not function as simple linear supply chains. Instead, they operate as decentralized, multi-layered nodes where information and hardware are abstracted through intermediary jurisdictions to mask the ultimate end-user.
To understand the mechanics of this operation, one must analyze the three structural components that allow such networks to persist despite intense federal oversight: jurisdictional arbitrage, technical dual-use obfuscation, and the financial decoupling of the transaction.
The Triad of Proliferation Logistics
Modern arms trafficking relies on a tripartite structure that minimizes the footprint of the primary actors while maximizing the reach of the procurement request.
1. Jurisdictional Arbitrage
Traffickers select transit points based on the regulatory friction present in each territory. In this specific Sudanese-Iranian case, the network exploits the distance between U.S. export controls and the enforcement capabilities of the African Sahel. The objective is to move high-value components from a high-regulation environment (the U.S.) to a low-oversight environment (Sudan), which serves as a staging ground for the final transfer to Iranian interests. This strategy relies on the Probability of Detection (P_d) being significantly lower in the transshipment phase than in the initial acquisition phase.
2. Dual-Use Technical Obfuscation
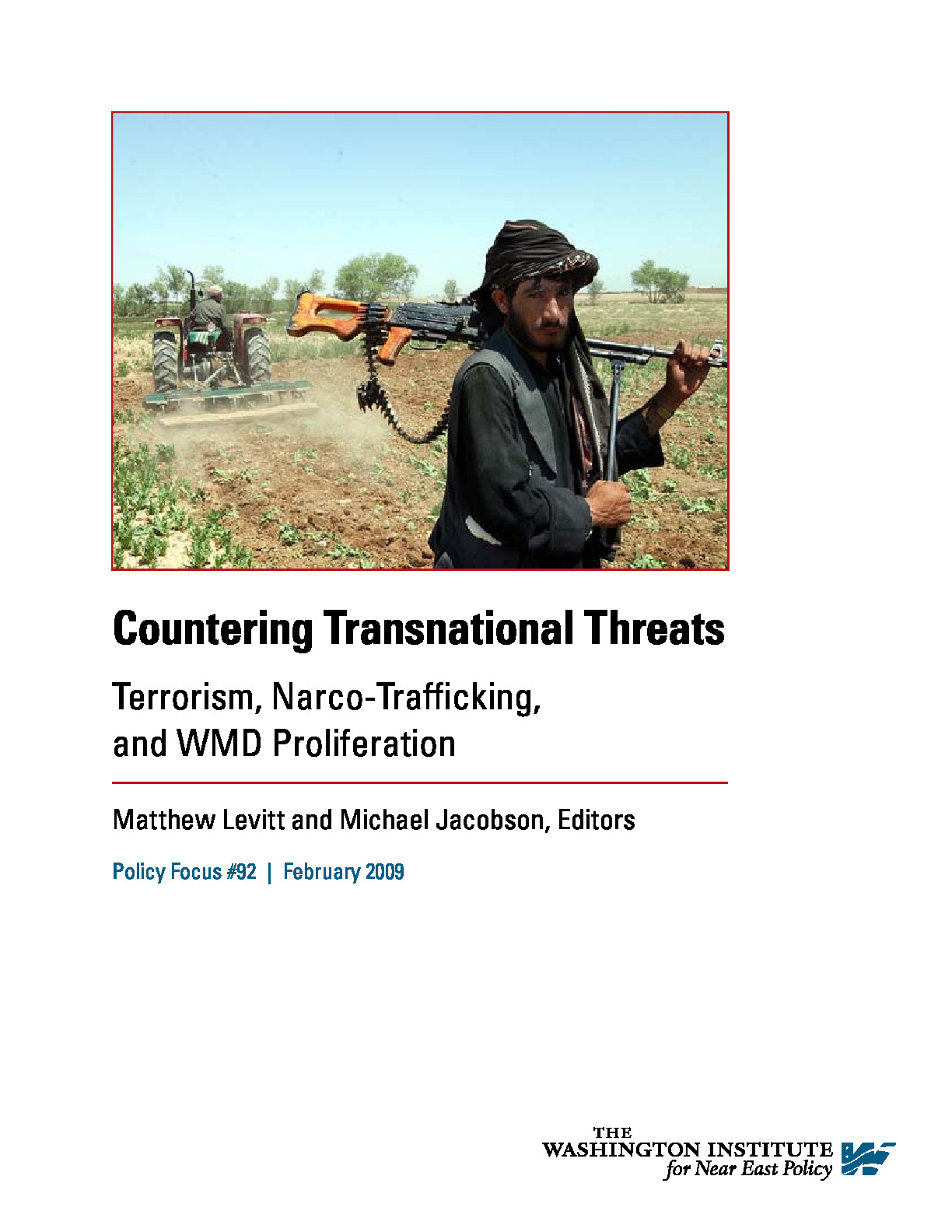
The technology targeted in these operations often falls into the category of "dual-use" items—hardware that has both civilian and military applications. By mislabeling high-spec sensors, drone components, or communication encryption hardware as "commercial electronics" or "industrial equipment," traffickers lower the alert threshold for customs officials. The procurement of components for Unmanned Aerial Vehicles (UAVs) is a primary focus. These items are the backbone of modern asymmetric warfare, providing low-cost, high-impact surveillance and strike capabilities that Sudan and Iran have historically integrated into their joint defense doctrine.
3. Financial Decoupling
The movement of money rarely follows the movement of goods. Traffickers utilize "hawala" systems, front companies, and increasingly, non-transparent digital assets to settle accounts. By ensuring the financial trail ends in a shell corporation in a non-extradition jurisdiction, the network insulates the organizers from the physical risks taken by the "mules" or procurement agents on the ground.
Quantifying the Procurement Friction
The success of a clandestine export operation is defined by the Net Success Rate (NSR), which can be modeled as a function of the regulatory environment and the sophistication of the concealment methods.
$$NSR = (1 - P_i) \times (1 - P_c) \times (1 - P_f)$$
Where:
- $P_i$ is the probability of detection at the initial point of sale.
- $P_c$ is the probability of seizure during customs transit.
- $P_f$ is the probability of the financial trail being flagged by anti-money laundering (AML) protocols.
In the case of the Sudanese-Iranian axis, the probability of detection is historically suppressed by utilizing individuals who possess valid residency or citizenship in the target export country. These individuals serve as the "clean" interface for the transaction, leveraging their legal status to establish commercial credibility with defense manufacturers.
The Role of Sudan as a Proliferation Conduit
Sudan occupies a specific strategic position in the Iranian defense strategy. While Iran possesses significant domestic manufacturing capabilities, it lacks access to certain high-end Western-integrated circuits and specialized materials that are critical for long-range precision. Sudan provides the geographic and political cover necessary to receive these goods.
The relationship functions as a technology-for-influence swap. Iran provides Sudan with technical military assistance and training, while Sudan provides the physical "blind spot" in the global surveillance net. This allows for the assembly and testing of systems away from the prying eyes of the International Atomic Energy Agency (IAEA) or other Western intelligence bodies.
Bottlenecks in the Iranian Supply Chain
The Iranian defense sector faces three primary bottlenecks that these illicit networks are designed to solve:
- Micro-circuitry Shortages: Iran’s domestic chip production cannot match the reliability or miniaturization of Western-made semiconductors.
- Material Science Gaps: High-temperature alloys and carbon fibers required for missile airframes and engine components are difficult to synthesize in-house under heavy sanctions.
- Sensor Calibration: Advanced optics and GPS-hardened receivers are required to overcome electronic warfare (EW) countermeasures deployed by regional rivals.
Operational Failures and the Logic of Detection
When a trafficking network is compromised, it is rarely due to a single "smoking gun." Instead, it is the result of pattern-matching anomalies within the Department of Commerce and Department of Justice databases.
The investigation into the woman charged in this case likely followed a "pull-back" analysis. Once a suspicious shipment was flagged—potentially due to a mismatch between the buyer's reported business activity and the technical specifications of the hardware ordered—federal agents worked backward through her communication logs. This process identifies the Node Density of the network—how many other actors she was in contact with and what roles they played in the logistical chain.
The failure points in these operations are frequently human rather than technical. Agents often exhibit "signature behaviors," such as:
- Using inconsistent shipping manifests.
- Rapidly rotating bank accounts with unusual wire transfer patterns from high-risk regions.
- Direct communication with known intelligence assets in the target country.
The Strategic Logic of UAV Proliferation
The hardware sought in these transactions frequently centers on the expansion of the "Shahed" family of loitering munitions. These systems have fundamentally altered the cost-to-benefit ratio of modern conflict. A UAV costing $20,000 can successfully neutralize a defensive system or infrastructure node worth millions.
The Iranian government’s pursuit of Western components for these systems is a rational economic choice. It is cheaper to smuggle a high-quality Western sensor than it is to build a lower-quality version domestically that may fail in a contested environment. This creates a Clandestine Procurement Loop where the sanctioned state continuously monitors the global market for specific part numbers that fill their technical gaps.
Regulatory Countermeasures and Systemic Limitations
The U.S. government responds to these threats through a combination of Entity List expansions and "Know Your Customer" (KYC) requirements for defense contractors. However, these systems face inherent limitations:
- The Velocity of Rebranding: Front companies can be dissolved and reconstituted in hours.
- The Scale of Global Trade: Monitoring every crate of "electronics" leaving a major port like Los Angeles or Newark is a statistical impossibility.
- The Complexity of Modern Hardware: Many parts required for military drones are indistinguishable from those used in the high-end hobbyist or industrial drone markets.
The burden of enforcement has shifted from physical border inspections to data-driven foresight. Agencies now employ predictive modeling to identify buyers whose profiles match the characteristics of previous proliferation agents. This includes looking for new entities with high capital influx but low historical operational data.
The Displacement Effect of Sanctions
Sanctions do not stop the flow of technology; they increase the Transaction Cost of that technology. By forcing Iran to use smugglers and intermediaries, the U.S. effectively imposes a "smuggling tax" on their defense budget. This tax manifests in three ways:
- Price Premiums: Traffickers charge 300% to 500% over market value for sanctioned goods.
- Logistical Lag: Goods that could be shipped in days take months to navigate through "safe" jurisdictions.
- Reliability Risk: The clandestine nature of the transport means hardware is often mishandled, leading to higher failure rates in the field.
The charging of a single individual is a tactical success, but it triggers a biological response in the network. Much like a hydra, the network will likely "deaden" the compromised node and reroute its procurement through a new, untested individual. The strategic priority for Western intelligence is not just arresting the mule, but identifying the financial switchboard that funded the operation.
Strategic Playbook for Counter-Proliferation
To disrupt these networks permanently, the focus must shift from the hardware to the logistical infrastructure.
- Targeting the Transit Hubs: Increasing diplomatic pressure on specific transit points in East Africa to implement more rigorous end-use monitoring.
- Hardware Fingerprinting: Implementing unique physical or digital signatures on high-end components that allow for tracing even after the product has been integrated into a larger system.
- Financial Isolation of Facilitators: Moving beyond individual arrests to sanction the accounting firms and legal entities in third-party countries that provide the "white-label" corporate shells used by traffickers.
The Sudanese-Iranian axis remains a critical threat because it allows a sanctioned regime to maintain a technological edge through the exploitation of globalized trade. The containment of this threat requires a recognition that the "war" is being fought in the databases of shipping firms and the ledgers of offshore banks, far from the actual kinetic battlefield.
Investments should be prioritized in real-time supply chain telemetry. By integrating AI-driven anomaly detection directly into the export licensing process, the window for jurisdictional arbitrage can be narrowed. The goal is to make the cost of illicit procurement so high that the sanctioned state is forced to rely on inferior domestic substitutes, thereby degrading their military effectiveness over a sustained period.